Posts matching: Archives

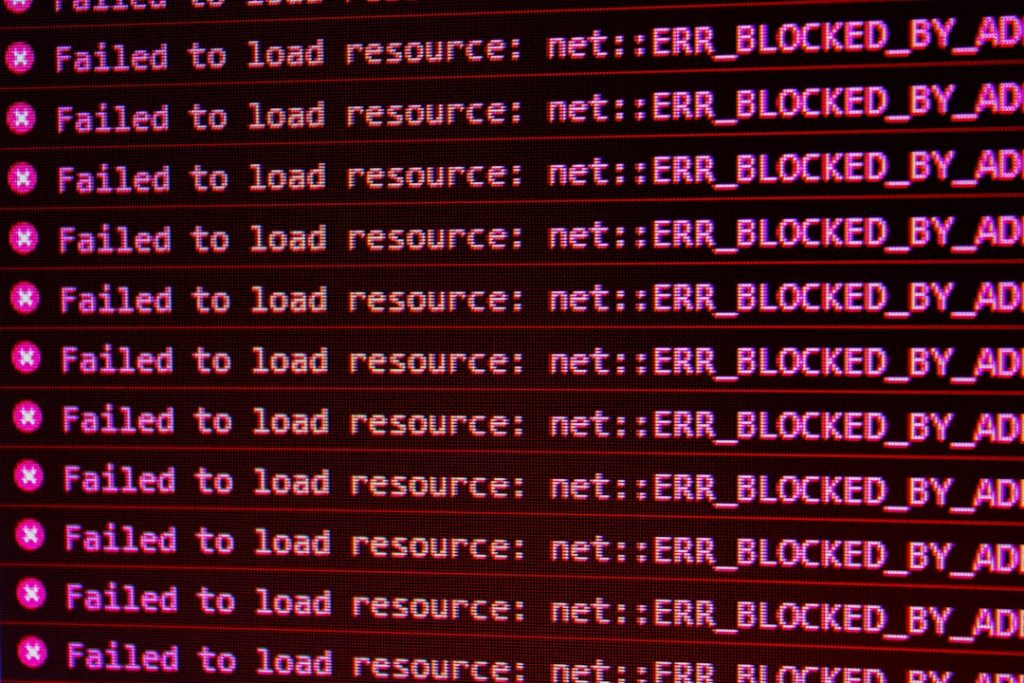
Firewall vs Antivirus: Understanding Your Security Stack Needs
!a close up of a network with wires connected to it
Cybercrime hit a devastating milestone in 2024: $16.6 billion in losses were reported to the FBI alone, a staggering 33 percent surge from the year before. Yet even against that backdrop, one of the most persistent myths in digital security is ...
Read More

Data Center Space Planning: Maximizing Your Infrastructure ROI
The digital economy runs on physical space - and that space has never been more contested. In 2025, colocation vacancy in North America declined to a new all-time low of 1.4%, as AI and hyperscale occupiers raced to secure power and capacity. If your organization is making decisions about data ce...
Read More

IT Staff Shortage Crisis: How Companies Are Adapting in 2026
The numbers tell an unambiguous story: by 2026, 90% of organizations worldwide will feel the pain of the IT skills crisis, costing as much as $5.5 trillion in delays, quality issues, and revenue loss, according to IDC. That's not a forecast to file away - it's a present-day reality reshaping boar...
Read More
Server Crash Data Recovery: What Every Business Should Know
Server downtime is not a theoretical risk. It is an operational certainty: unexpected outages are a common challenge, with 37% of servers experiencing at least one unexpected outage in recent years. When a server crashes, the fallout can be immediate, severe, and, without the right plan in place,...
Read More

Is Your Server Room a HIPAA Lawsuit Waiting to Happen?
When most executives in healthcare, finance, or legal services hear the words “SOC 2” or “HIPAA,” their minds immediately go to the digital realm. ...
Read More

Why Your Office Server Closet Isn’t a Data Center
Maybe you’re even sitting twenty feet away from it right now: that small, windowless room, originally designed to hold extra boxes of copier paper ...
Read More

